Key Administration Service
페이지 정보

본문
KMS Service | Key Management Service | Pico [2024]
Go to Home » KMSPico KMS Service is used to activate Microsoft Windows & Microsoft Office products. It ensures that the software program is legally bought from Microsoft.
KMS Service is used to activate Microsoft Windows & Microsoft Office products. It ensures that the software program is legally bought from Microsoft.
KMS is used for quantity license activation.
All companies, faculties & non-profits use this KMS service.
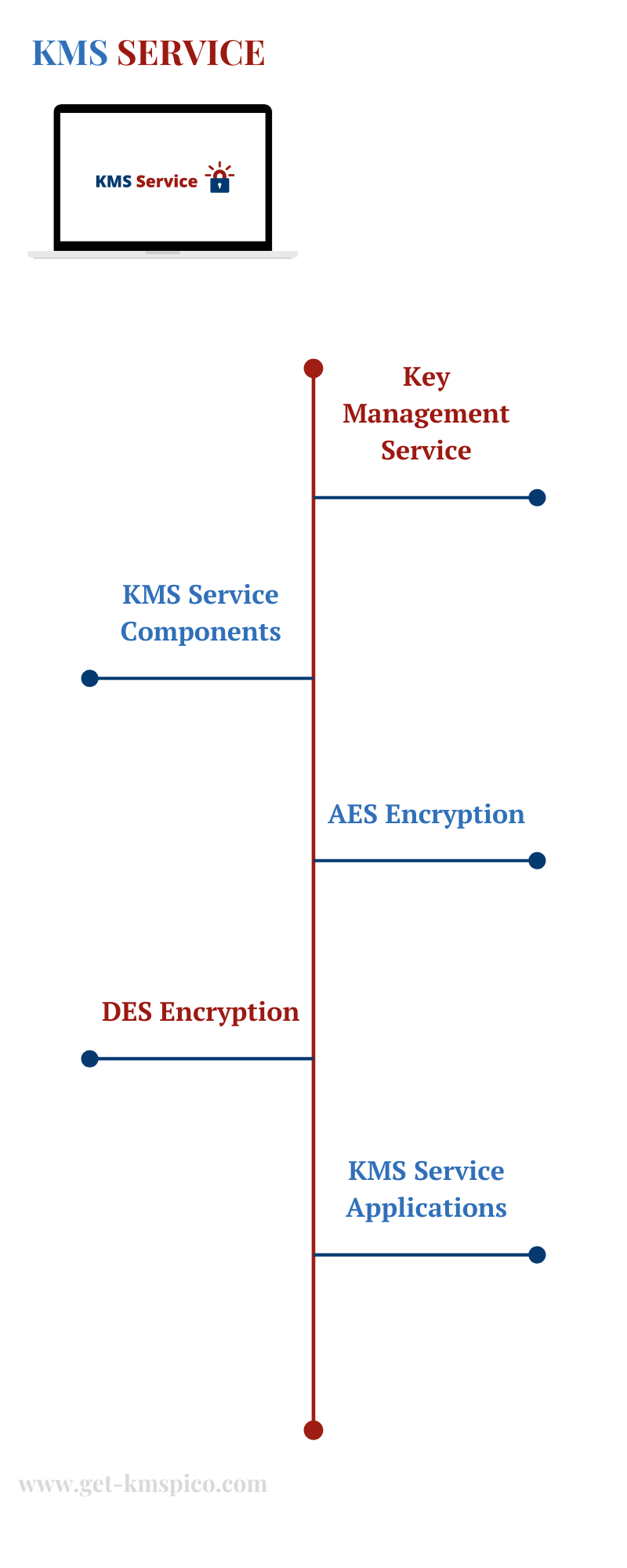
KMS Service
You will have some knowledge and also you need to protect it.Like perhaps a credit card or a social security quantity.
Additionally, you've an encryption key and an encryption program that might do AES encryption.
Many encryption algorithms are used.
If you are doing a normal Nationwide Institute of Standards and Expertise NIST sort of encryption, it may very well be DES (Information Encryption Customary).
The encryption key is the unique bit of data that is what protects your information.
It's a secret that you've to make sure it does not get misplaced.
KMS service is designed to create, protect, and deliver Encryption Keys.
Both by doing Encryption or Decryption tasks.
It is deployed on a typical server that you just would possibly discover in any IT pc room.
They are sometimes designed to be more safe.
KMS Service Elements
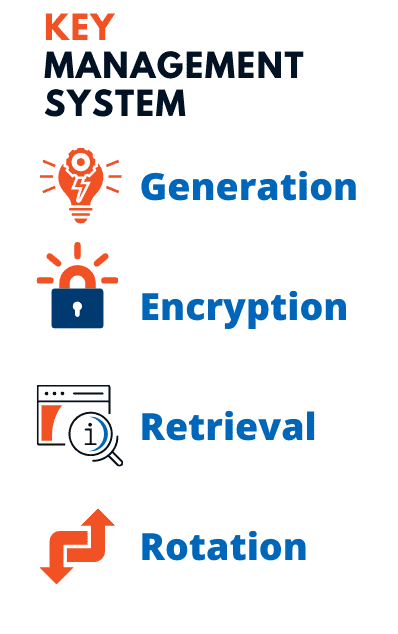 There are four major components of a KMS Service.
There are four major components of a KMS Service.- Era of Encryption Keys
- Encryption of Encryption Keys
- Retrieval of Encryption Keys
- Rotation of Encryption Keys
Encryption Key Technology
Era is a crucial part.It is comparatively onerous to generate an excellent unpredictable encryption key.
It makes use of a random number generator to generate them, to make sure it's unpredictable.
To do this, Cryptographically safe or True Random Number Generators are deployed.
As soon as it's generated then it has to be saved on a pc.
Storing it on a server is one other job in itself.
That is saved in an encrypted format with some special keys referred to as Encryption Keys.
Now that we now have obtained the key generated and securely saved, we now have to have the ability to retrieve them.
We should be capable of convey them into our Windows mainframe or Linux applications.
In order that we can use them to encrypt our data.
Encryption Key Retrieval
Key Retrieval is another essential element of the KMS Service.It is done securely.
In other words, we don’t need that key to go over the network.
In order that it could not be uncovered to a loss.
Retrieval is often finished with either safe SSL or TLS-type periods.
It is wrapped in a safe package and moved over the community.
Encryption Key Rotation
Changing a key is called Key Rotation.Many compliance laws require that keys needs to be modified periodically, perhaps each 90 days or yearly.
Being ready to vary the outline or the activation and expiration dates of keys can also be an necessary component of a system.
If you create the keys maybe you don’t need to use them for a particular interval.
Likewise, if they're lost or compromised, you could need to revoke them or make them unusable.
You might even want to delete or destroy them.
 These are a few of the basic Functions.
These are a few of the basic Functions.
They're created at the National Institute of Standards and Know-how NIST.
If you want to know extra about them, just Google NIST SP 800-53.
Right here is an entire discussion about the important thing life cycle.
That is all pretty well outlined now.
What we have now talked about thus far in phrases of making, activating, expiring, revoking, and deleting keys.
It is all a part of the key life cycle process.
It should usually offer you the power to manage and entry those keys.
You have to make sure that only the fitting persons are utilizing them.
You have to know, how a lot of them you could have, what are their names, and what are their attributes.
So Question is one other necessary element of the system.
It will present a mechanism for backing up and actual-time mirroring.
KMS Service Emulator
- 이전글Understanding Why People Get Horny 24.11.01
- 다음글The Growing Importance of Video Conferencing for Connecting Across Distances 24.11.01
댓글목록
등록된 댓글이 없습니다.